The theme this year has been big vulnerabilities in common services or shared libraries - places where one bug might affect lots and lots of programs and devices. First it was a flaw in OpenSSL, the library that enables secure communication with websites around the world. Next came a flaw in Bash shell, a widely used Unix shell much like the Windows command line. Now it's ntpd, the Network Time Protocol service.
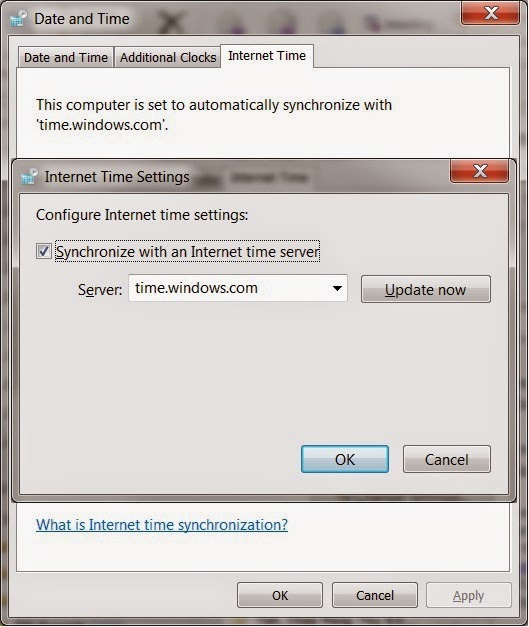
NTP can be envisioned as the timekeeper of the Internet. It is the way systems synchronize their time throughout a network, and it's the reason you don't have to manually set the clock on your computer. On your Windows PC, there is an "Internet Time" tab that is by default enabled. Your PC periodically queries an Internet clock for the current time, and sets your local clock to the correct time.
On a home PC, setting the clock is merely a convenience. On a corporate network, it is a necessity. Some authentication services require that both the client and the server believe it to be the same time. When the US Congress decided to change the dates for Daylight Savings Time a few years back, more than a few businesses awoke that Monday to dozens if not hundreds of service calls from employees that could not log on because their computer had not received the update with the new dates.
In forensic analysis, time is critical in analyzing the sequence of events in an incident. Network attacks don't usually involve only one computer; if each device on a network has a different time, it is difficult if not impossible to accurately track the timeline. Thus businesses use ntp to synchronize time across the entire organization.
On Friday, ntp.org disclosed a number of vulnerabilities in all versions of NTP prior to 4.2.8. The most serious vulnerability is identified as CVE-2014-9295: Stack buffer overflow. With this flaw, an attacker can send a specially-crafted packet to a server or router running ntpd, the NTP daemon (or service), and cause the server or router to run code of the attacker's choosing. This potentially can allow an attacker to take complete control of the vulnerable device.
The bad news is, like Heartbleed and Shellshock, there is no one-size-fits-all patch. NTP is used in many devices, by many manufacturers. In some cases end users can update the ntp package within a product, but in many cases we are dependent on the developers to release an update for their individual products.
The silver lining is that this affects devices listening for ntp packets. In other words, this affects servers and network routers, which are intended to listen for and provide a time service. It should not affect most laptops, PCs, smartphones, tablets, and other end-user devices.
So ... Server admins, Unix developers, network technicians, prepare for a busy time.
Cert.org is maintaining a list of affected products and their status (vulnerable, non-vulnerable, unknown.