TL;DR: Chrome has a nifty undocumented trick that makes proxying so much more useful when testing sites using HSTS or pinned certs: where the security warning screen doesn't give you an option to ignore, type "badidea" to continue anyway.
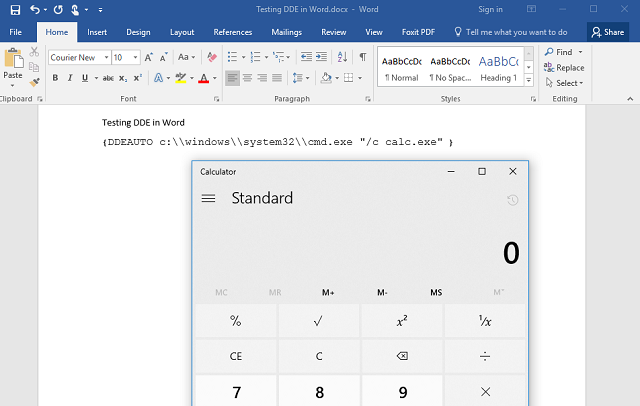
Browser makers have been raising the bar when it comes to website security, gradually moving toward a state where insecure websites stand out like a sore thumb. The result has been a steady increase in the proportion of websites that safeguard your private information while in transit between you and the web server. Google's Chrome in particular makes it especially challenging to use badly secured websites, with a variety of warning messages such as the image above.
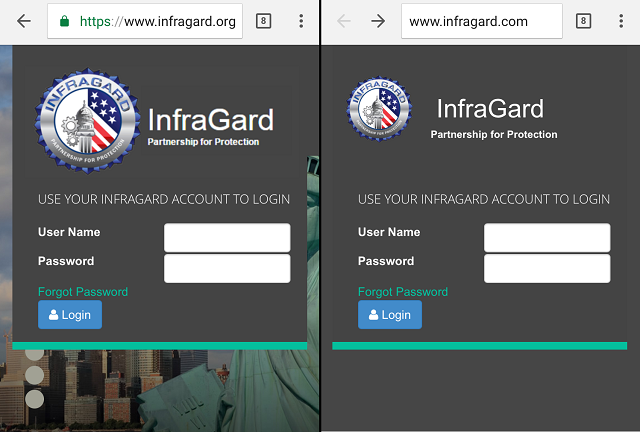
In the example above, the website in question has enabled HTTP Strict Transport Security, or HSTS, which tells browsers that it should only be accessed over a secure channel, and so to always use HTTPS. Essentially, the website tells browsers "don't ever come here again except over HTTPS."
In this case, the warning is slightly misleading: I am browsing to the site over HTTPS, but using a proxy to inspect what I am sending to the website. The proxy feature of Burp Suite allows me to send information to a secure website, but to catch and decrypt it before it leaves my computer, to see exactly what my browser is sending.
As a penetration tester or vulnerability researcher, it is very handy for making sure an application is not sending more data than I intend. It is also very handy for probing an application for data leaks and weaknesses. In this scenario, Chrome's helpful protection is less, well, helpful.
Thankfully, Google developers included an undocumented Easter Egg: typing the phrase "badidea" while that warning is on the screen, will clear the warning and proceed to the website.
A note to readers: this is a handy trick for researchers and penetration testers. Generally though, that warning is there for a reason. If you unexpectedly see a warning that your connection is not private - your connection is not private. If you are not intentionally man-in-the-middling your connection, the warning likely means either the website or your network is compromised. The technique I use for testing web applications is the same technique used by malicious hackers to eavesdrop when you connect to an "evil twin" hotspot mimicking the legitimate connection provided by your coffee shop or airport.
The moral? Unless you know what you are doing, bypassing Chrome's privacy warning is, well, a bad idea.