|
| Yahoo! accounts have very different security options depending on their origin. |
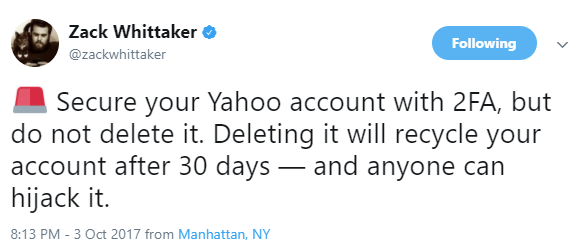
Zack Whittaker, security editor for ZDNet, had this to say:
That's good advice - if you can. Many cannot.
In 2002, Yahoo! and regional telecom company SBC launched a co-branded dial-up Internet service, and later added DSL as an early broadband offering. Three years later, SBC Communications bought AT&T, introducing a tangle of AT&T, SBC Global, and Yahoo! user IDs and email addresses.
Customers at the time were urged to merge their Yahoo!, AT&T, and sbcglobal.net accounts. Those long-time customers have since endured over a decade and a half in the forgotten hinterlands of Yahoo!.
To Zack's point, deleting a long-standing Yahoo! account is an easy knee-jerk reaction, but probably not the best of ideas. Email is often the back door to recovering access to everything else; if your Yahoo! account was ever added as the recovery account for a now-long-forgotten service, and you were to delete your Yahoo! account, 30 days from now anyone could recreate an account with the same email alias, and gain access to your forgotten services.
For a Yahoo! account created after the SBC/AT&T debacle, establishing two-factor authentication is a straightforward process: from the user profile icon, select "Account info."

Then provide a phone number to receive an extra password by SMS (text message). Those that have followed me long know that I am not a fan of SMS-based two-factor because it is becoming easier for malicious actors to intercept an SMS code. Ideally, you want the additional factor to be an authenticator app such as Duo or Google Authenticator, or a physical device such as a Yubikey or an RSA token. If SMS is all that a service offers though, it is still nominally better than a password alone.
So, about those merged AT&T/Yahoo! accounts
The Account Security tab for merged accounts looks just a bit different:

Those of us that ever had broadband Internet service through SBC Communications are completely out of luck.
OK, so now what?
My recommendations are:
- Whether you have a native Yahoo! account or a merged Yahoo!/AT&T account (even a dormant one), don't delete it. Set your password to the strongest you can get away with. Alas AT&T limits passwords to 24 characters, allows only hyphen and underscore as special characters - and if you violate these restrictions, it only informs you of one error at a time. Yahoo! native accounts in my limited testing do not limit password length or character choice.
- If you have a Yahoo! native account, set up two-step verification, as described above.
- If you have a merged account and cannot enable two-step verification, DON'T use that account as the email recovery for anything else. If your online banking or social media are protected by strong two-factor authentication, but uses a weak Yahoo! account as its backup, anyone that can phish your Yahoo! account password can gain full control over your bank accounts or your social media accounts. Your best bet is a new email account from a provider with strong security controls.