
Professional social engineer and open source intelligence expert Stephanie "@_sn0ww" Carruthers makes a living out of (mis)using what people and companies share publicly, so when she talks I listen. Her talk at the Lonestar Application Security conference in October was captivating in showing how such information can be used to infiltrate a business (in her case, for the purposes of showing the business their weaknesses and how to defend themselves against someone with actual malicious intent). She made an observation this week that sparked some lively discussion:
By the same token though, anyone with the link can read it.
So can anyone that takes a few seconds to craft a suitable Google query.
However, "don't do this" isn't exactly helpful. I've been through a couple of job searches recently. It's not always practical to seek employment while hiding out of sight. In many circles a positive "personal brand" can be a strong asset, and a personal brand cannot be developed entirely in the shadows. Australian security expert Troy Hunt has written several times about using the potential benefits of an online identity as a personal brand. I can assure you I did indeed share my resume publicly, in several forms and in several locations.
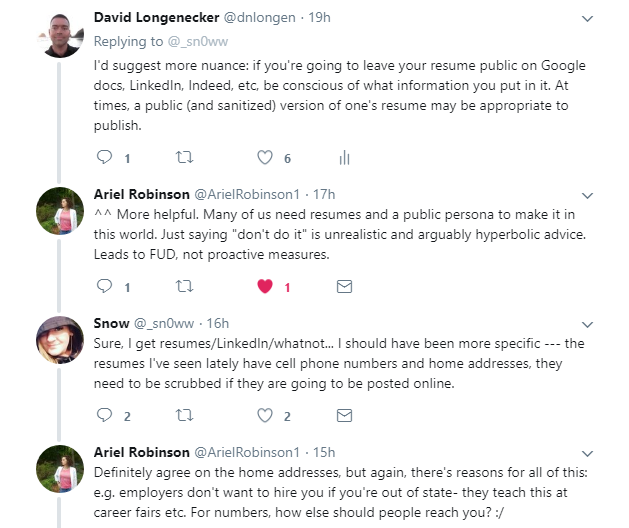
The key though is that I am conscious of what I share, and with whom. My public resume identifies my public social media aliases, where in the country I reside, enough detail about my work history to demonstrate my body of work without revealing specific products used by my former employers, and a way to contact me.
Throwaway email addresses and virtual phone numbers are great for this purpose.
There is a great parallel between this and social media. I've written before of the privacy decisions inherent in social media, and made the point that ill-advised sharing has cost many a person their job, their family, their freedom, or even their life. My approach is to decide for each social platform how I will use it - then tailor privacy settings along with what I share to that purpose.
Likewise, there is a parallel between this and consumer loyalty programs. Perhaps I may be willing to share some information with a business in exchange for freebies and "members only" specials. Or perhaps not. The point is, it's a conscious decision.
What works for me may not work for you, and what works for you may not be right for me - and that's great. We each have different priorities and different perspectives. Perhaps Jessie Irwin said it best: data privacy isn't about not sharing. Data privacy is sharing on my terms.
Data privacy means making a conscious decision about what data I share, with whom, and for what purpose. Which sounds an awful lot like the European General Data Privacy Regulation taking effect across the European Union next May.
So before you put your resume in a public share, or sign up for a customer loyalty program, or post on social media, or answer a survey, make sure you are sharing on your terms.

